For her seminal contributions to cryptography by innovating cryptanalysis methods to reveal weaknesses of widely used hash functions, which have enabled new generation of cryptographic hash function standards.
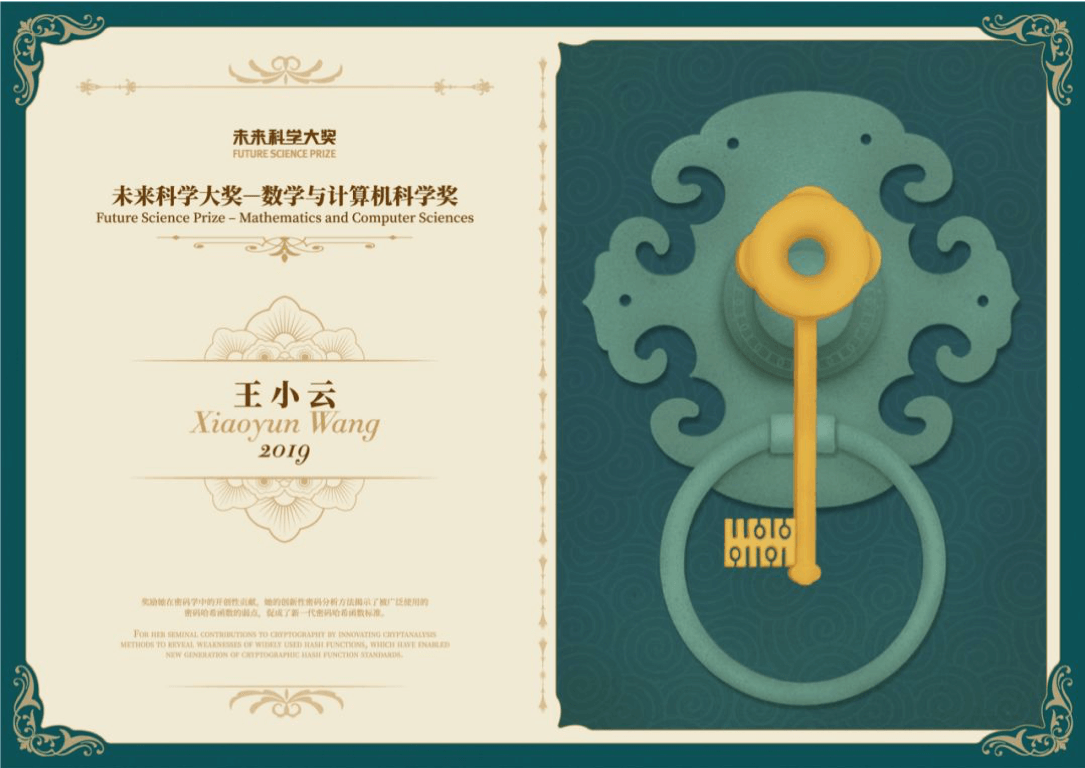
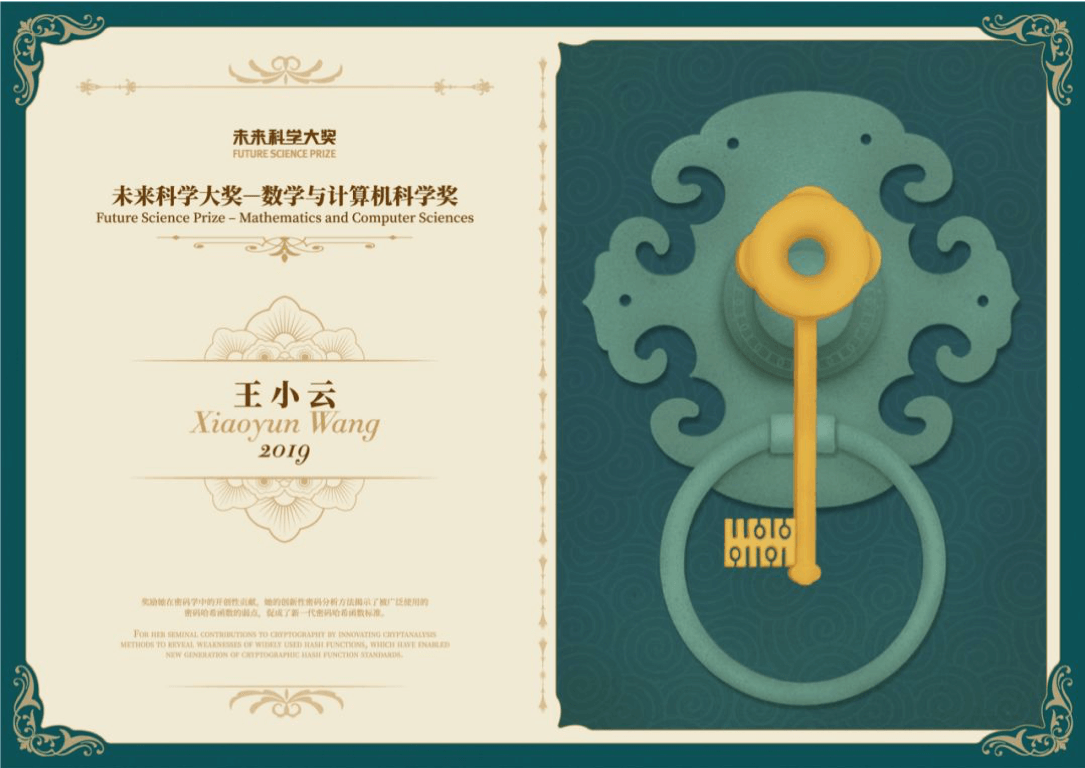
2019 The Mathematics and Computer Science Prize Laureate

Cryptographic hash functions are at the core of many, if not most, applications of cryptography such as digital signature schemes, Secure Sockets Layer (SSL), password validations, web certificates, information integrity, and block-chain. A cryptographic hash function takes some data as input and outputs a short digest, with an important property that is hard to find a “collision” or two pieces of distinct input data that hash to the same digest. If one could find a collision of a cryptographic hash function easily, all applications using it would be considered insecure.
Prof. Xiaoyun Wang developed a series of powerful cryptanalysis methods, especially bit-based modular differential cryptanalysis, for cryptographic hash functions. Her methods showed the fatal weaknesses of many previously considered secure cryptographic hash function standards, and revolutionized how to analyze and design new-generation standards. In 2004, Prof. Wang presented a novel analysis method called bit-based modular differential cryptanalysis, and demonstrated true collisions of MD5, a widely used cryptographic hash function for over a decade. This was a surprise result in the cryptography community at the time as MD5 had withstood over a decade of attacks from many other cryptographers. In 2005, she and her coauthors extended the method to attack several other well-known hash functions including MD4, RIPEMD, and HAVAL-128. In the same year, she and her collaborators published an approach to show that it was possible to find collisions of SHA-1, another widely used cryptographic hash function standard, with 2^69 and then further reduced to 2^63 operations. Previously, most researchers were convinced that it was not feasible to find collisions with fewer than 280 operations. While it was too costly in 2005 to carry out their attacks on SHA-1 in practice, others successfully executed attacks on SHA-1 on the Google cloud 12 years later using a method that built on Prof. Wang’s approach.
Her work triggered the phase out of MD5 and SHA-1 hash functions from almost all software systems including the largest software systems such as Windows and Linux. Her work also propelled and helped the development of new-generation of cryptographic hash functions including SHA-3, BLAKE2 and SM3. Prof. Wang herself led the design of SM3, a Chinese national standard which has been widely used by many Chinese software products since 2010.